Jungle flasher feezing on lite on key extraction
Jungle flasher feezing on lite on key extraction
I tried flashing my first lite on today and I cant seem to get the key/dump the other files
-I have the via drivers disabled and renamed(not deleted)
-portIO32 is installed
-CK3 probe drivers are installed
-My drive is recognized in JF as well as my com port
-ck3 probe gets the green lite when its on the R707 hole
Once Im in JF with the tray half open and I click the get dummy ect..button it will read the key 1-2 times then JF freezes. My comp doesnt lock up, JF just freezes. When I go to close the program I get the windows "this program is not responding" message. I end the program and my comp still runs fine. The most key extractions I have managed to get is 4 after several trys and several comp restarts.
I tried using one other usb com port and it didnt work much better and Ive tried different versions of JF. Any suggestions? Ive read/watched the tuts several times and followed them to the T. I cant seem to find any posts with anyone with a similar problem. Im about to scrap JF all together and give iprep a shot.
If its having this much trouble just dumping the drive, I dont know if I even want to see what happens when I get to the erase point.
-I have the via drivers disabled and renamed(not deleted)
-portIO32 is installed
-CK3 probe drivers are installed
-My drive is recognized in JF as well as my com port
-ck3 probe gets the green lite when its on the R707 hole
Once Im in JF with the tray half open and I click the get dummy ect..button it will read the key 1-2 times then JF freezes. My comp doesnt lock up, JF just freezes. When I go to close the program I get the windows "this program is not responding" message. I end the program and my comp still runs fine. The most key extractions I have managed to get is 4 after several trys and several comp restarts.
I tried using one other usb com port and it didnt work much better and Ive tried different versions of JF. Any suggestions? Ive read/watched the tuts several times and followed them to the T. I cant seem to find any posts with anyone with a similar problem. Im about to scrap JF all together and give iprep a shot.
If its having this much trouble just dumping the drive, I dont know if I even want to see what happens when I get to the erase point.
- dalecheesy
- Ally of Robinhood

- Posts: 1379
- Joined: Sat Jan 24, 2009 8:08 pm
- Location: Sunderland UK
Re: Jungle flasher feezing on lite on key extraction
Strange one, are you powering the ck3 with an onboard molex or one in your tower? Might be worth using a spare atx supply if you have one. failing that yeah give iprep a try as it's a doddle to use but make sure you reboot into windows after the dump and save the dump to a few different locations (maybe email it to yourself)
You'll also need an r232 cable for your ck3 as iprep doesn't work through usb though.
You'll also need an r232 cable for your ck3 as iprep doesn't work through usb though.

Re: Jungle flasher feezing on lite on key extraction
Yes Im using a molex power plug from my comps power supply. I dont currently have a spair supply, but I may try to borrow one.The ck3 and the probe both seem to have power the entire time though (LEDs are lit) I think I may give team xecuters ck3 tool a try to see if it can get the key and dump. If that still fails then Im going to give iprep a shot.
Thanks for the advice. Anyone else ever ran into this specific problem.
Thanks for the advice. Anyone else ever ran into this specific problem.
- HaGGardSmurf
- Ally of Robinhood

- Posts: 4088
- Joined: Tue Feb 03, 2009 9:46 am
- Location: Alberta, Canada
Re: Jungle flasher feezing on lite on key extraction
See if you can get your hands on a rs232 cable.
Sounds like your CK3 and probe are working fine, to me it sounds like your having some kind of usb problems...
Also, what os are you on? If XP, what SP and what .net framework?
Sounds like your CK3 and probe are working fine, to me it sounds like your having some kind of usb problems...
Also, what os are you on? If XP, what SP and what .net framework?
Re: Jungle flasher feezing on lite on key extraction
Im using xp sp2 with .net 2.0. Im at work right now, but I belive its 2.0 I rounded up a rs232 cable here at work today. I was kinda thinking it might be a usb communication issue also. Do I need service pack 3.
- HaGGardSmurf
- Ally of Robinhood

- Posts: 4088
- Joined: Tue Feb 03, 2009 9:46 am
- Location: Alberta, Canada
Re: Jungle flasher feezing on lite on key extraction
Well try your rs232 cable first, if you still get freezing, you may want to try SP3 & .net framework 3.5.
Re: Jungle flasher feezing on lite on key extraction
I ended up getting the key. I had an external drive hooked up to one of my usb ports in the back of my comp. Once I unhooked it I got the key and the dump. But I was a little concerned about some of the info that was showing in the running log of JF. When it showed all the stings there seemed to be alot of .... or spaces and ...x..... or .....h.....(see log below) I was worried the data was corrupt, especially after having issues extracting it with the probe.
I went and watched coffrees tut very closely and paused at the times when he was saving all his files in JF and the strings looked similar. So I assume im ok to move on and spoof??? I figured I would ask here just to be safe.
IF that seems normal to you.. can I just load my dummy.bin in my source and my IX6 in my target next time I get into JF and proceed from there. I dont need to dump again right? thanks again for the help.
JungleFlasher 0.1.64 Beta
Session Started Tue Jul 28 17:20:42 2009
This is a 32 bit process running on a 32 bit CPU
PortIO is installed and running.
Found 4 I/O Ports.
Found 1 Com Ports.
Found 8 windows drives D: E: F: G: H: I: J: L:
Found 2 CD/DVD drives D: J:
Sending DVDKey request to I/O port 0xDC00 and COM3
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
Extracted drive key matched 6 times.
Key data saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Key.bin
0000: 05 80 00 32 5B 00 00 00 - 50 4C 44 53 20 20 20 20 ...2[...PLDS
0010: 44 47 2D 31 36 44 32 53 - 20 20 20 20 20 20 20 20 DG-16D2S
0020: 37 34 38 35 30 43 41 30 - 41 31 44 36 30 38 43 47 74850CA0A1D608CG
0030: 38 31 36 39 30 39 30 30 - 54 50 30 20 20 20 00 00 81690900TP0 ..
0040: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
0050: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
Inquiry String saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Inquiry.bin
0000: C0 85 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
0010: 00 00 00 00 44 36 30 38 - 43 47 38 31 36 39 30 39 ....D608CG816909
0020: 30 30 54 50 30 20 20 20 - 00 00 00 00 00 00 34 37 00TP0 ......47
0030: 35 38 43 30 20 20 4C 50 - 53 44 20 20 20 20 47 44 58C0 LPSD GD
0040: 31 2D 44 36 53 32 20 20 - 20 20 20 20 20 20 20 20 1-D6S2
0050: 20 20 20 20 20 20 20 20 - 20 20 20 20 20 20 00 00 ..
0060: 00 00 00 0B 00 00 00 04 - 00 02 06 00 00 00 00 00 ................
0070: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
0080: 03 00 78 00 78 00 E3 00 - 78 00 00 00 00 00 00 00 ..x.x...x.......
0090: 00 00 00 00 00 00 00 00 - 02 02 00 00 68 00 00 00 ............h...
00A0: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
00B0: 20 20 00 00 ..
Identify String saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Identify.bin
0000: 44 36 30 38 43 47 38 31 - 36 39 30 39 30 30 54 50 D608CG81690900TP
0010: 30 20 20 20 FF FF FF FF - 38 44 30 36 30 33 34 36 0 ....8D060346
0020: 31 37 44 35 31 34 58 58 - 41 30 FF FF 53 34 50 38 17D514XXA0..S4P8
0030: 34 31 31 30 30 30 30 30 - 30 32 36 38 38 31 00 00 41100000026881..
0040: FF FF FF FF FF FF FF FF - FF FF FF FF 41 31 FF FF ............A1..
Dummy.bin file saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Dummy.bin
Loading DVDkey source file
Inquiry string found
Identify string found
DVD key found @ 0xA030 key is F4E7C423B10A418E63A284339F812BF0
Firmware is a Lite-On Dummy OSIG: PLDS DG-16D2S 7485
Firmware type is: DVDKey32 extract
Key added to database
I went and watched coffrees tut very closely and paused at the times when he was saving all his files in JF and the strings looked similar. So I assume im ok to move on and spoof??? I figured I would ask here just to be safe.
IF that seems normal to you.. can I just load my dummy.bin in my source and my IX6 in my target next time I get into JF and proceed from there. I dont need to dump again right? thanks again for the help.
JungleFlasher 0.1.64 Beta
Session Started Tue Jul 28 17:20:42 2009
This is a 32 bit process running on a 32 bit CPU
PortIO is installed and running.
Found 4 I/O Ports.
Found 1 Com Ports.
Found 8 windows drives D: E: F: G: H: I: J: L:
Found 2 CD/DVD drives D: J:
Sending DVDKey request to I/O port 0xDC00 and COM3
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
................ Serial Data looks ok, key returned: F4E7C423B10A418E63A284339F812BF0
Extracted drive key matched 6 times.
Key data saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Key.bin
0000: 05 80 00 32 5B 00 00 00 - 50 4C 44 53 20 20 20 20 ...2[...PLDS
0010: 44 47 2D 31 36 44 32 53 - 20 20 20 20 20 20 20 20 DG-16D2S
0020: 37 34 38 35 30 43 41 30 - 41 31 44 36 30 38 43 47 74850CA0A1D608CG
0030: 38 31 36 39 30 39 30 30 - 54 50 30 20 20 20 00 00 81690900TP0 ..
0040: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
0050: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
Inquiry String saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Inquiry.bin
0000: C0 85 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
0010: 00 00 00 00 44 36 30 38 - 43 47 38 31 36 39 30 39 ....D608CG816909
0020: 30 30 54 50 30 20 20 20 - 00 00 00 00 00 00 34 37 00TP0 ......47
0030: 35 38 43 30 20 20 4C 50 - 53 44 20 20 20 20 47 44 58C0 LPSD GD
0040: 31 2D 44 36 53 32 20 20 - 20 20 20 20 20 20 20 20 1-D6S2
0050: 20 20 20 20 20 20 20 20 - 20 20 20 20 20 20 00 00 ..
0060: 00 00 00 0B 00 00 00 04 - 00 02 06 00 00 00 00 00 ................
0070: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
0080: 03 00 78 00 78 00 E3 00 - 78 00 00 00 00 00 00 00 ..x.x...x.......
0090: 00 00 00 00 00 00 00 00 - 02 02 00 00 68 00 00 00 ............h...
00A0: 00 00 00 00 00 00 00 00 - 00 00 00 00 00 00 00 00 ................
00B0: 20 20 00 00 ..
Identify String saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Identify.bin
0000: 44 36 30 38 43 47 38 31 - 36 39 30 39 30 30 54 50 D608CG81690900TP
0010: 30 20 20 20 FF FF FF FF - 38 44 30 36 30 33 34 36 0 ....8D060346
0020: 31 37 44 35 31 34 58 58 - 41 30 FF FF 53 34 50 38 17D514XXA0..S4P8
0030: 34 31 31 30 30 30 30 30 - 30 32 36 38 38 31 00 00 41100000026881..
0040: FF FF FF FF FF FF FF FF - FF FF FF FF 41 31 FF FF ............A1..
Dummy.bin file saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Dummy.bin
Loading DVDkey source file
Inquiry string found
Identify string found
DVD key found @ 0xA030 key is F4E7C423B10A418E63A284339F812BF0
Firmware is a Lite-On Dummy OSIG: PLDS DG-16D2S 7485
Firmware type is: DVDKey32 extract
Key added to database
- HaGGardSmurf
- Ally of Robinhood

- Posts: 4088
- Joined: Tue Feb 03, 2009 9:46 am
- Location: Alberta, Canada
Re: Jungle flasher feezing on lite on key extraction
Yep, thats perfect. Thats how it should be. Basically what your seeing is the hex and dec data of the FW. Hex is the:
0000: xx xx xx xx xx xx
(the hex are the numbers & letters in the xx xx xx format)
and the dec are the dots and the other data thats not in the xx xx xx format. Its nothing really to be concerned about... If you are able to dump the key, its pretty safe to assume your other data was dumped successfully...
0000: xx xx xx xx xx xx
(the hex are the numbers & letters in the xx xx xx format)
and the dec are the dots and the other data thats not in the xx xx xx format. Its nothing really to be concerned about... If you are able to dump the key, its pretty safe to assume your other data was dumped successfully...
Re: Jungle flasher feezing on lite on key extraction
Great. Im going to go ahead with the rest then. I'll let you know how it goes. Appreciate the help.
Re: Jungle flasher feezing on lite on key extraction
Well I got all the way to the end and JF froze on the write. The spoof went fine. I got the 1 sec trick, but it only worked half way the 1st time. I got the 072 status but it only listed the vendor id and device id. No name size or type. So I hit erase again (which might have been my big mistake) and it worked fine and listed every thing. So I thanked god and thought I was in the clear. Then JF froze after writing only the 1st sector of the 1st bank.
Now of course my drive is locked up. It wont eject and wont show up in JF. Just like when I was extracting, only JF froze during the write and not my entire comp.
Can I spoof a samMS28 with my lite on info?? I have an extra samMS2 laying around and I still have the key,dummy,ID and inquiry.bin files.
If not I guess I am going to have to figure out the Iprep recovery method. This has been a nightmare of a flash. I think Im done with JF. I also grabbed the wrong rs232 cable at work. I took one with 2 female ends rather than male.
Now of course my drive is locked up. It wont eject and wont show up in JF. Just like when I was extracting, only JF froze during the write and not my entire comp.
Can I spoof a samMS28 with my lite on info?? I have an extra samMS2 laying around and I still have the key,dummy,ID and inquiry.bin files.
If not I guess I am going to have to figure out the Iprep recovery method. This has been a nightmare of a flash. I think Im done with JF. I also grabbed the wrong rs232 cable at work. I took one with 2 female ends rather than male.
Re: Jungle flasher feezing on lite on key extraction
OMG this nightmare continues. I realized I dont even have a rs232 port on my comp, so the iprep idea is out the window. So I spoofed my old samsung drive with my liteon.dummy(as source) and IX6 samsung firmware(as target). Every thing went fine and I thought it was done....I put it in the xbox. It played my original non-backup game just fine. But it doesnt seem to like backups at all(all back ups I know are good and playable) Some give me open tray errors, some give me disc is dirty errors and some load and act like they will play by going into the game intro or menus only to give me read errors before I get to actually playing the game. One even said "mixed media disc"
So I dont know what to think at this point. The samsung drive is a drive taken from a rrod console so I dont know how good it is to begin with. Only things I can come up with are
A. The lense is dirty, but that doesnt make sense since it plays originals just fine
B. I messed up the spoofing. and I should have used IX6 lite on firmware rather than the samsung
I was going off this tut
http://www.youtube.com/watch?v=y8jcG9FD ... re=related" onclick="window.open(this.href);return false;
Any advice at this point would be great. I have one other sammy drive I could try but I dont think the drive is the real problem. Any advice is much appreciated, this is getting ridiculous heres the JF log
JungleFlasher 0.1.64 Beta
Session Started Tue Jul 28 23:14:49 2009
This is a 32 bit process running on a 32 bit CPU
PortIO is installed and running.
Found 4 I/O Ports.
Found 0 Com Ports.
Found 8 windows drives D: E: F: G: H: I: J: L:
Found 2 CD/DVD drives D: J:
Sending Vendor Intro to port 0xDC00
Parallel flash found with Status 0x70
Sending Device ID request to port 0xDC00
Manufacturer ID: 0xBF
Device ID: 0xB6
Flash Name: SST(SST39SF020)
Flash Size: 262144 bytes
Getting Status from port 0xDC00
Parallel flash found with Status 0x70
Reading Bank 0: ................
Reading Bank 1: ................
Reading Bank 2: ................
Reading Bank 3: ................
Samsung Dump file saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmy Sam spoofed to liteon\samsung dunp\SAM-OFW.bin
Loading MTK_Flash source file
Inquiry string found
Identify string found
DVD key found @ 0x40EC key is 9796D9D819107C24328B6712172E23C2
Firmware is Samsung OSIG: TSSTcorpDVD-ROM TS-H943Ams28
Firmware type is: iXTREME1.6-12x-FINAL-TS-H943A
Key database updated
Loading Source File L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Dummy.bin
Inquiry string found
Identify string found
DVD key found @ 0xA030 key is F4E7C423B10A418E63A284339F812BF0
Firmware is a Lite-On Dummy OSIG: PLDS DG-16D2S 7485
Firmware type is: DVDKey32 extract
Loading target file L:\Documents and Settings\Admin\Desktop\360 Tools\Samsung 1.6 firmware\ix16-samsung.bin
Target File MD5 hash is: 23f5a368839dfc10dabb8231ba64567a
Genuine Samsung iXtreme 1.6
Inquiry string found
Identify string found
DVD key found @ 0x40EC key is 77777777777777777777777777777777
Firmware is Samsung OSIG: TSSTcorpDVD-ROM TS-H943Ams28
Firmware type is: iXTREME1.6-12x-FINAL-TS-H943A
Spoofing Target
DVD Key copied to target
Inquiry string copied from Source to Target
Identify string copied from Source to Target
Identify string copied reversed
Target spoofed as: PLDS DG-16D2S 7485
Target f/w saved as: L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmy Sam spoofed to liteon\samsung dunp\Sam-spoofed to liteon-FW.bin
Getting Status from port 0xDC00
Parallel flash found with Status 0x70
Sending Chip Erase request to port 0xDC00
Blank Test !
Reading Bank 0: ................
Reading Bank 1: ................
Reading Bank 2: ................
Reading Bank 3: ................
Blank verified OK !
Getting Status from port 0xDC00
Parallel flash found with Status 0x70
Writing target buffer to flash
Erasing Bank 0: ................
Writing Bank 0: ................
Erasing Bank 1: ................
Writing Bank 1: ................
Erasing Bank 2: ................
Writing Bank 2: ................
Erasing Bank 3: ................
Writing Bank 3: ................
Flash Verification Test !
Reading Bank 0: ................
Reading Bank 1: ................
Reading Bank 2: ................
Reading Bank 3: ................
Write verified OK !
Sending Vendor Outro to port 0xDC00
So I dont know what to think at this point. The samsung drive is a drive taken from a rrod console so I dont know how good it is to begin with. Only things I can come up with are
A. The lense is dirty, but that doesnt make sense since it plays originals just fine
B. I messed up the spoofing. and I should have used IX6 lite on firmware rather than the samsung
I was going off this tut
http://www.youtube.com/watch?v=y8jcG9FD ... re=related" onclick="window.open(this.href);return false;
Any advice at this point would be great. I have one other sammy drive I could try but I dont think the drive is the real problem. Any advice is much appreciated, this is getting ridiculous heres the JF log
JungleFlasher 0.1.64 Beta
Session Started Tue Jul 28 23:14:49 2009
This is a 32 bit process running on a 32 bit CPU
PortIO is installed and running.
Found 4 I/O Ports.
Found 0 Com Ports.
Found 8 windows drives D: E: F: G: H: I: J: L:
Found 2 CD/DVD drives D: J:
Sending Vendor Intro to port 0xDC00
Parallel flash found with Status 0x70
Sending Device ID request to port 0xDC00
Manufacturer ID: 0xBF
Device ID: 0xB6
Flash Name: SST(SST39SF020)
Flash Size: 262144 bytes
Getting Status from port 0xDC00
Parallel flash found with Status 0x70
Reading Bank 0: ................
Reading Bank 1: ................
Reading Bank 2: ................
Reading Bank 3: ................
Samsung Dump file saved to L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmy Sam spoofed to liteon\samsung dunp\SAM-OFW.bin
Loading MTK_Flash source file
Inquiry string found
Identify string found
DVD key found @ 0x40EC key is 9796D9D819107C24328B6712172E23C2
Firmware is Samsung OSIG: TSSTcorpDVD-ROM TS-H943Ams28
Firmware type is: iXTREME1.6-12x-FINAL-TS-H943A
Key database updated
Loading Source File L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmys Drive\Dummy.bin
Inquiry string found
Identify string found
DVD key found @ 0xA030 key is F4E7C423B10A418E63A284339F812BF0
Firmware is a Lite-On Dummy OSIG: PLDS DG-16D2S 7485
Firmware type is: DVDKey32 extract
Loading target file L:\Documents and Settings\Admin\Desktop\360 Tools\Samsung 1.6 firmware\ix16-samsung.bin
Target File MD5 hash is: 23f5a368839dfc10dabb8231ba64567a
Genuine Samsung iXtreme 1.6
Inquiry string found
Identify string found
DVD key found @ 0x40EC key is 77777777777777777777777777777777
Firmware is Samsung OSIG: TSSTcorpDVD-ROM TS-H943Ams28
Firmware type is: iXTREME1.6-12x-FINAL-TS-H943A
Spoofing Target
DVD Key copied to target
Inquiry string copied from Source to Target
Identify string copied from Source to Target
Identify string copied reversed
Target spoofed as: PLDS DG-16D2S 7485
Target f/w saved as: L:\Documents and Settings\Admin\Desktop\360 Drives\Jimmy Sam spoofed to liteon\samsung dunp\Sam-spoofed to liteon-FW.bin
Getting Status from port 0xDC00
Parallel flash found with Status 0x70
Sending Chip Erase request to port 0xDC00
Blank Test !
Reading Bank 0: ................
Reading Bank 1: ................
Reading Bank 2: ................
Reading Bank 3: ................
Blank verified OK !
Getting Status from port 0xDC00
Parallel flash found with Status 0x70
Writing target buffer to flash
Erasing Bank 0: ................
Writing Bank 0: ................
Erasing Bank 1: ................
Writing Bank 1: ................
Erasing Bank 2: ................
Writing Bank 2: ................
Erasing Bank 3: ................
Writing Bank 3: ................
Flash Verification Test !
Reading Bank 0: ................
Reading Bank 1: ................
Reading Bank 2: ................
Reading Bank 3: ................
Write verified OK !
Sending Vendor Outro to port 0xDC00
- HaGGardSmurf
- Ally of Robinhood

- Posts: 4088
- Joined: Tue Feb 03, 2009 9:46 am
- Location: Alberta, Canada
Re: Jungle flasher feezing on lite on key extraction
Sounds like your samsung drive is bad. Open it up, and clean the laser, I bet it will play a couple backups...
I swapped out a stock hit 47 cause it wouldnt play anything. I cleaned the laser flashed it and tried, it played just about all originals, but no backups. I think it played 1, but none of the others I tested. I know all the backups are good, because I play them on my console's...
Well you have dumped your drive already, so you dont need the rs232 port. Also, erasing twice wouldn't have done anything to cause the freezing. (If drivers are not disabled)
Here is cofree's guide for recovering your lite-on:
viewtopic.php?f=195&t=3226" onclick="window.open(this.href);return false;
I swapped out a stock hit 47 cause it wouldnt play anything. I cleaned the laser flashed it and tried, it played just about all originals, but no backups. I think it played 1, but none of the others I tested. I know all the backups are good, because I play them on my console's...
Well you have dumped your drive already, so you dont need the rs232 port. Also, erasing twice wouldn't have done anything to cause the freezing. (If drivers are not disabled)
Here is cofree's guide for recovering your lite-on:
viewtopic.php?f=195&t=3226" onclick="window.open(this.href);return false;
Re: Jungle flasher feezing on lite on key extraction
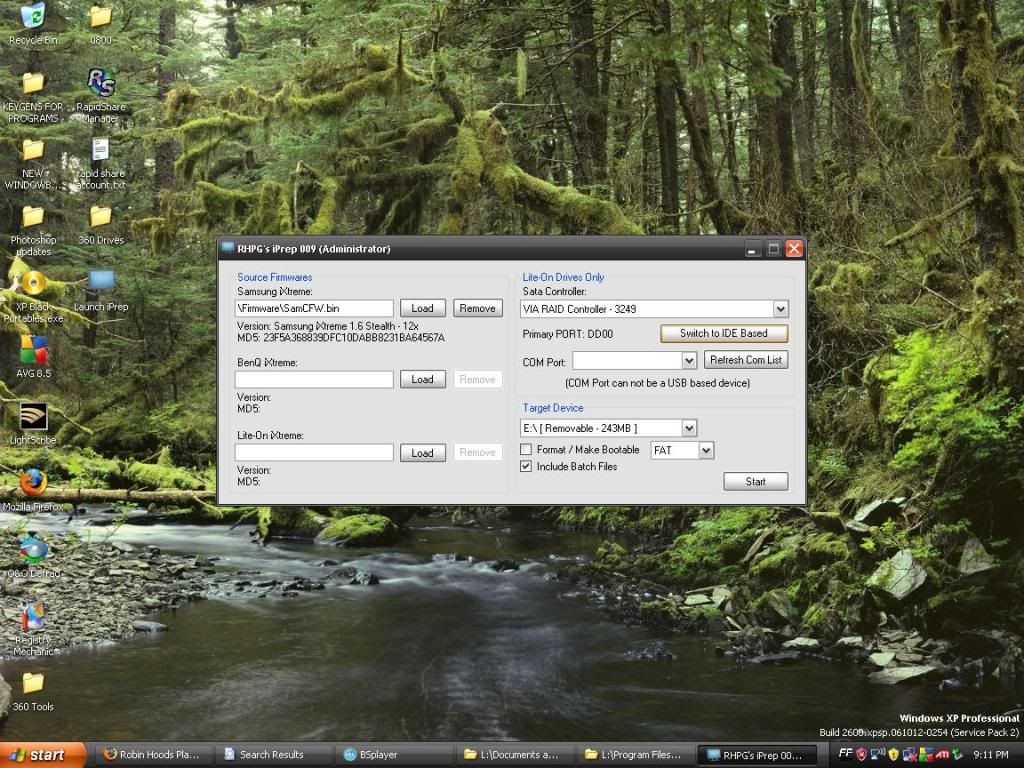
I am going to see if I can get coffrees recover tut to work for me. Im still pretty new to iprep. Im using iprep 009. I just figured out the updating defintions deal. Couple of questions
- In the source area are you supposed to load in the IX6. rar or the IX6.bin it seems to take either, Im thinking it doesnt matter and it just gets the info it needs either way.
-It recognizes my via sata controller, but it lists The primary port as DD00. Every time I have used jungle flasher my drives show up on the DC00 port(I dont see an option to change the port). Is this going to be a problem. My main hard drive is on one of my mother boards sata slots and I dont want to screw that up(if that even has anything to do with this part)
-In coffrees tut he says to "put a patch in MTK Flash" I dont see this option in iprep 009
-Do I keep the "include batch files" box checked.
Again man, I really appriciate the help. heres a screen shot of what ive got set up so far
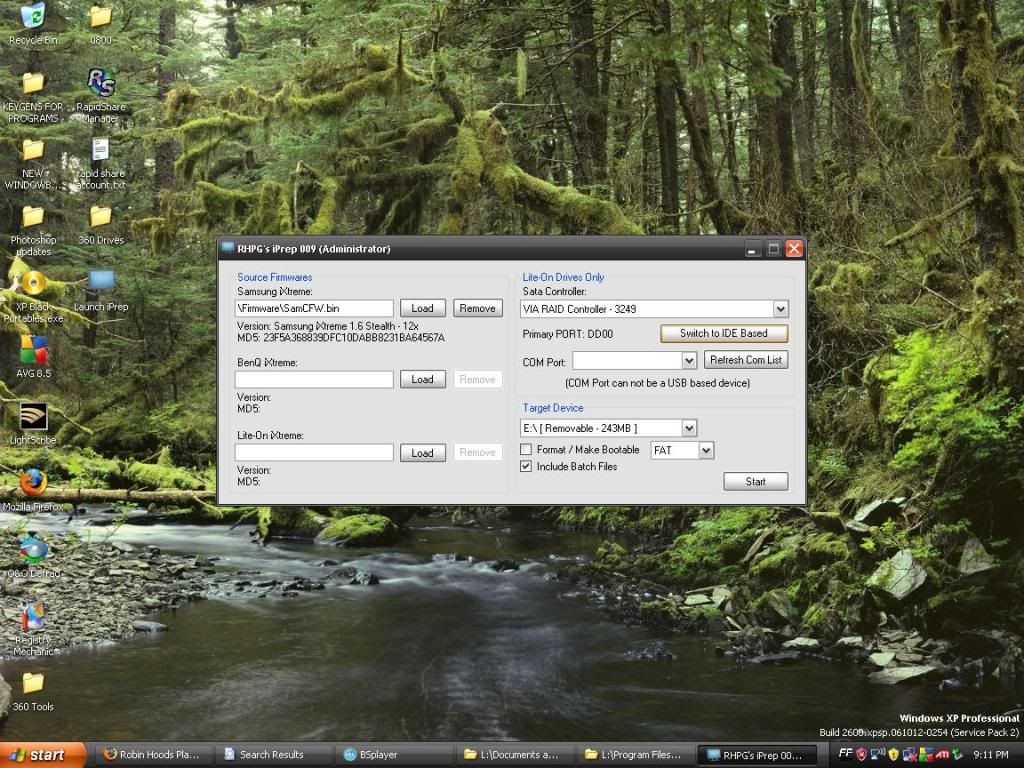
*that large drive isnt my actual flash stick, its just what was on there when I took the screen shot*
- In the source area are you supposed to load in the IX6. rar or the IX6.bin it seems to take either, Im thinking it doesnt matter and it just gets the info it needs either way.
-It recognizes my via sata controller, but it lists The primary port as DD00. Every time I have used jungle flasher my drives show up on the DC00 port(I dont see an option to change the port). Is this going to be a problem. My main hard drive is on one of my mother boards sata slots and I dont want to screw that up(if that even has anything to do with this part)
-In coffrees tut he says to "put a patch in MTK Flash" I dont see this option in iprep 009
-Do I keep the "include batch files" box checked.
Again man, I really appriciate the help. heres a screen shot of what ive got set up so far
*that large drive isnt my actual flash stick, its just what was on there when I took the screen shot*
Re: Jungle flasher feezing on lite on key extraction
Well it looks like you were right. The lense was just dirty. I had another samsung 360 that has rrod that I was planning on sending in. The one that I tried spoofing into the lite on 360 had writing on the case, so I decided I would attempt to swap the guts, so I could still send the one crappy drive back with a clean case and spoof the good one into the lite on 360.
I got to taking apart the case for the crappy drive. It came off super easy. Just 4 screws and the front and back were off. I flipped over the drive and I saw that the laser was right there! So I just cleaned it off with a cloth and got rid of all the other dust and crap that was in the drive, popped it in the 360 and booyah....it plays every thing flawlessly!!!
So my five night flashing saga is over. I still fail at lite on's though. Even after attempting a JF flash(failed write with drivers disabled) an Iprep flash(failed write) and several dosflash recovery attempts(failed write)
All in all though it was a great learning experience. I learned 2 new flash methods, learned drive spoofing and learned how to clean a lense.
I still wonder what is up with me not being able to write to lite ons though. Ive only done 2 other sammys but they went perfect. I think my via card might be kinda iffy. I dont know. But again. Thank You! for all the expert advice
I got to taking apart the case for the crappy drive. It came off super easy. Just 4 screws and the front and back were off. I flipped over the drive and I saw that the laser was right there! So I just cleaned it off with a cloth and got rid of all the other dust and crap that was in the drive, popped it in the 360 and booyah....it plays every thing flawlessly!!!
So my five night flashing saga is over. I still fail at lite on's though. Even after attempting a JF flash(failed write with drivers disabled) an Iprep flash(failed write) and several dosflash recovery attempts(failed write)
All in all though it was a great learning experience. I learned 2 new flash methods, learned drive spoofing and learned how to clean a lense.
I still wonder what is up with me not being able to write to lite ons though. Ive only done 2 other sammys but they went perfect. I think my via card might be kinda iffy. I dont know. But again. Thank You! for all the expert advice
Re: Jungle flasher feezing on lite on key extraction
Update:
The samsung drive that I spoofed and put in the lite on 360 is having disk read errors again, so I went back to the old lite on and all it took to flash it was using a different sata port on my via card. I wasted soo much time trying other methods. I cant believe I didnt try a different port before going through every method and program in the book to fix it.
The samsung drive that I spoofed and put in the lite on 360 is having disk read errors again, so I went back to the old lite on and all it took to flash it was using a different sata port on my via card. I wasted soo much time trying other methods. I cant believe I didnt try a different port before going through every method and program in the book to fix it.

